-
-
The Problems Nobody Talks About in Security Consulting
There’s a version of security consulting that looks great on paper. A pentest gets scoped, executed,…
-

The Play-Pretend Problem
Walk into any large enterprise’s security team and ask them to show you what they’ve built.…
-

The Tool-Dependency Problem
Every CISO I’ve ever spoken to has a version of the same conversation at least once…
-
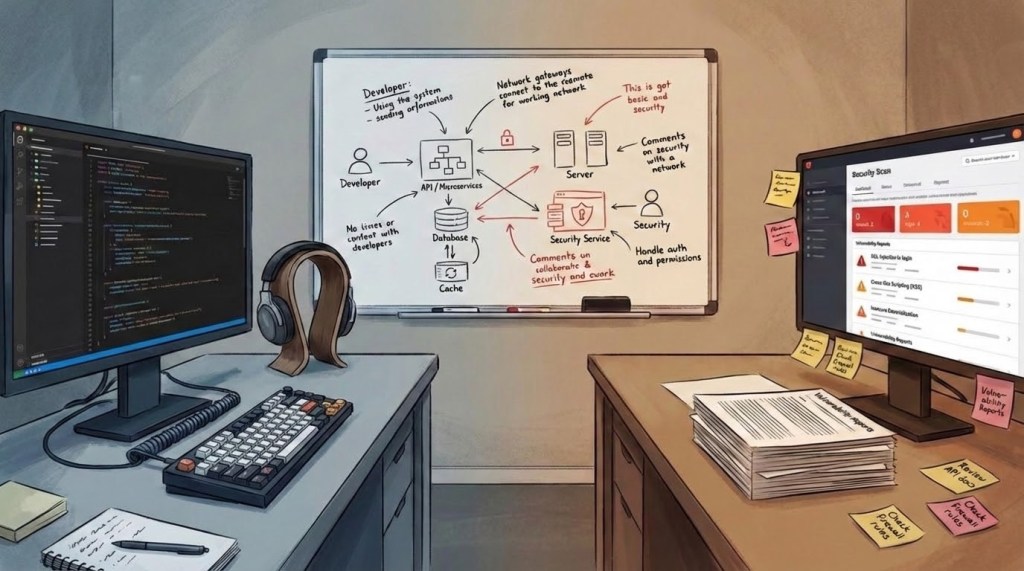
The Dev-Sec Friction Problem
There’s a meeting that happens in almost every organisation with both a security team and a…
-
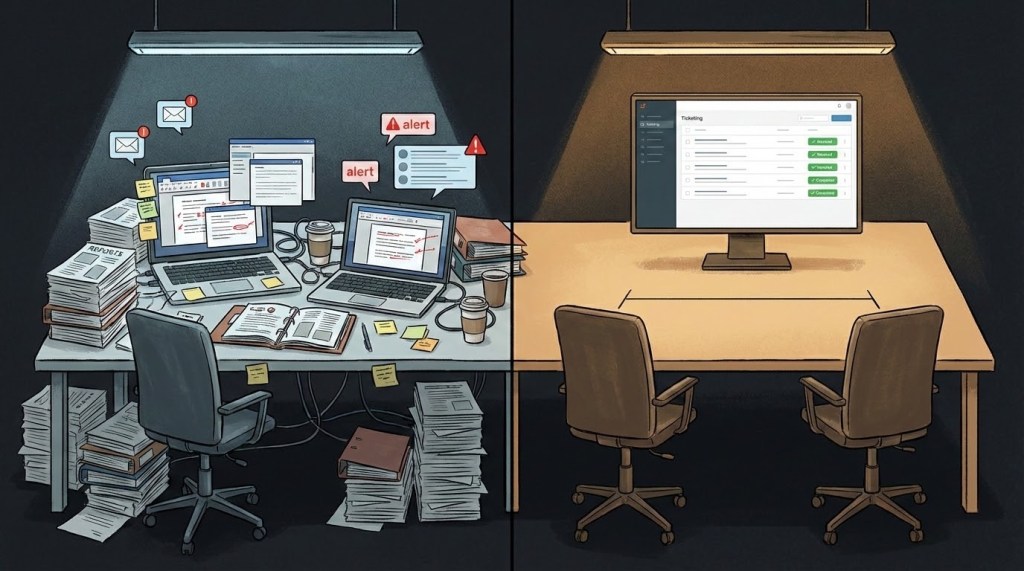
The Pentesting Delivery Problem
Ask any pentester how their findings get delivered and the answer is almost always the same:…
-

The One Who Held the Sacred
He spoke of passion that kneels in flame –not the kind that pleads.He carried fire as…
-
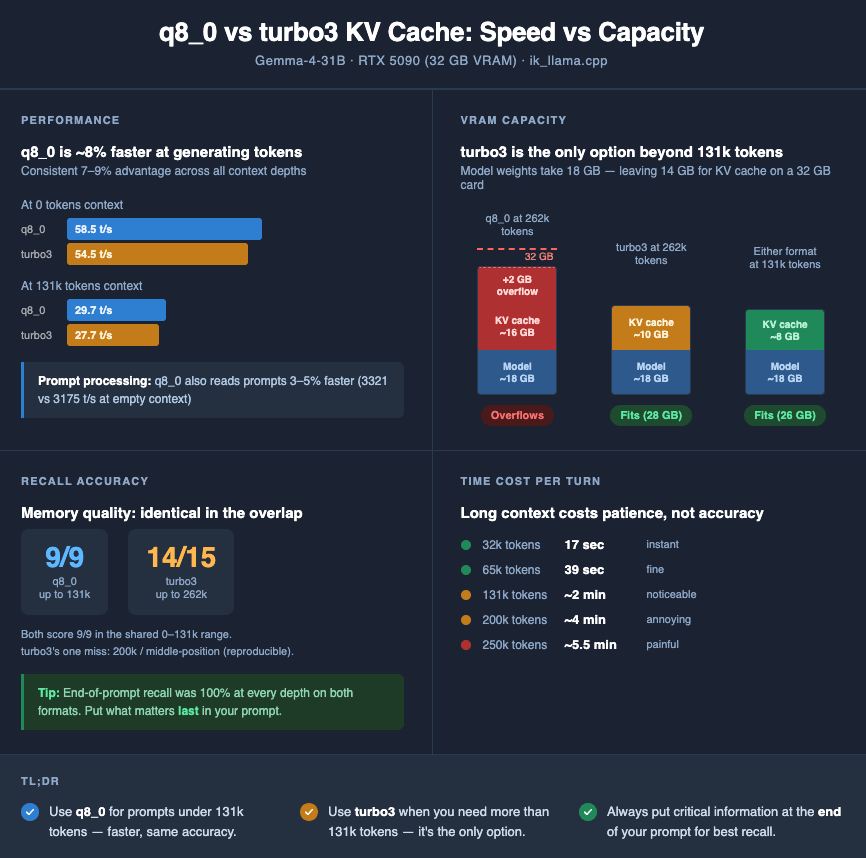
AI Didn’t Find the CVE. The Workflow Did
Everyone’s arguing about whether AI “works” in security. Wrong question. The right question is: are you building…
-
Subscribe
Subscribed
Already have a WordPress.com account? Log in now.